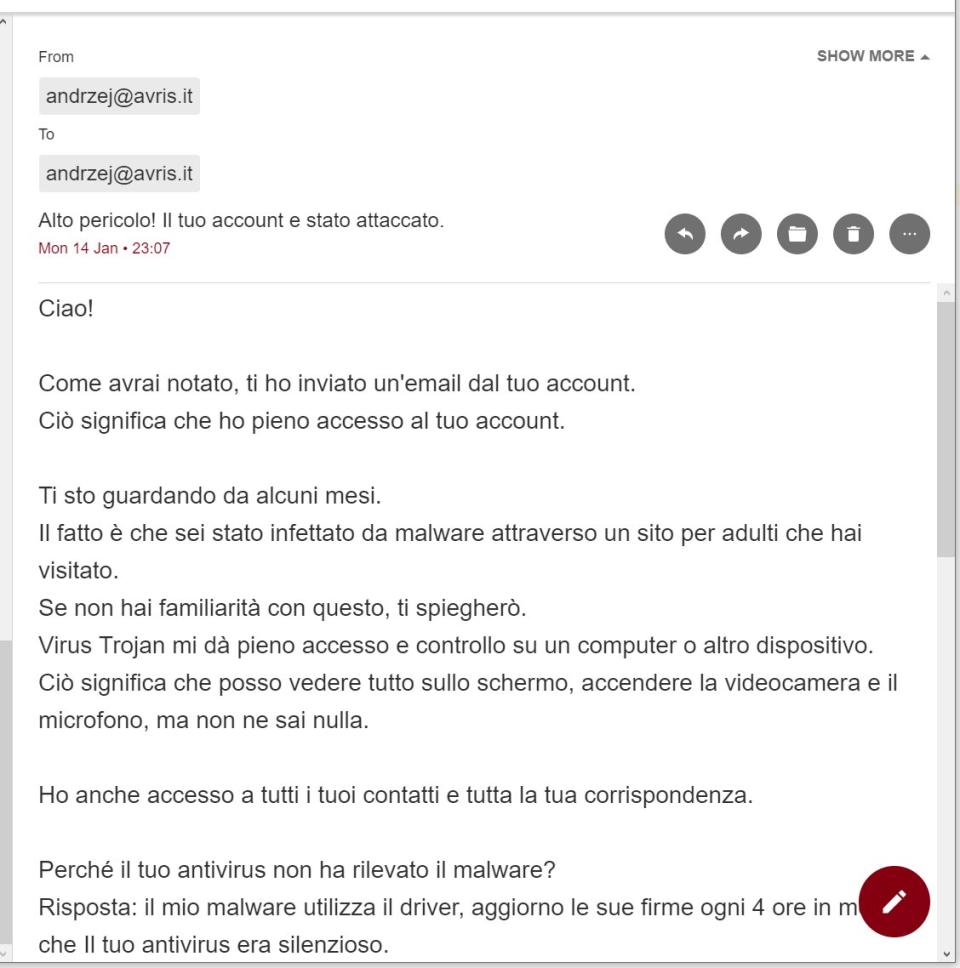
Did anyone receive a message recently that contained a video of me watching porn?
Because apparently I was being blackmailed that all my contacts would receive it, if I don’t pay 202€ in BTC. Alas, I didn’t check the spam folder, so I’d missed the deadline a week ago 
- If they really had full access to my computer, they’d know that I almost never use Italian... Only to talk to some old friends once in a blue moon, and to laugh at all the spammers who assume that owning a “.it” domain automatically makes you Italian.
- If they really had full access to my computer, or even checked out my public posts on social media, they’d know I don’t give a shit about someone seeing me naked or masturbating.
- Blackmailing someone with that is the most obvious choice: almost everyone watches porn & masturbates, and most people are (inexplicably) ashamed of it.
- They didn’t attach ANY proof whatsoever. Not a piece of a video, not a single URL from browser history, not a screenshot. Not even naming my OS or browser. I have no idea, which of my computers they claim to have attacked
- Sending an email from my own address to myself is given as a “proof” that they control my computer. The thing is, via SMTP you can send an email with ANY valid email in the “From” field. Most clients will deem it unreliable though and put it in spam – exactly as has happened here.
- They claim to have been “observing me for a couple of months”. Well, to get enough porn & masturbation blackmail material on me, they wouldn’t need more than a day
- “Malware was undetectable by the antivirus, because driver” is a BS talk for people who don’t know shit about computers. They’ve been watching me for months, they should know I know my shit about computers
- Most importantly: the deadline is over already. And nothing?
Despite so many red flags people seem to be buying this bullshit, apparently. Those criminals have received 4,5 BTC already (~14k€). Within A WEEK!
Please, educate yourself about cybersecurity, people... And don’t panic!
Update
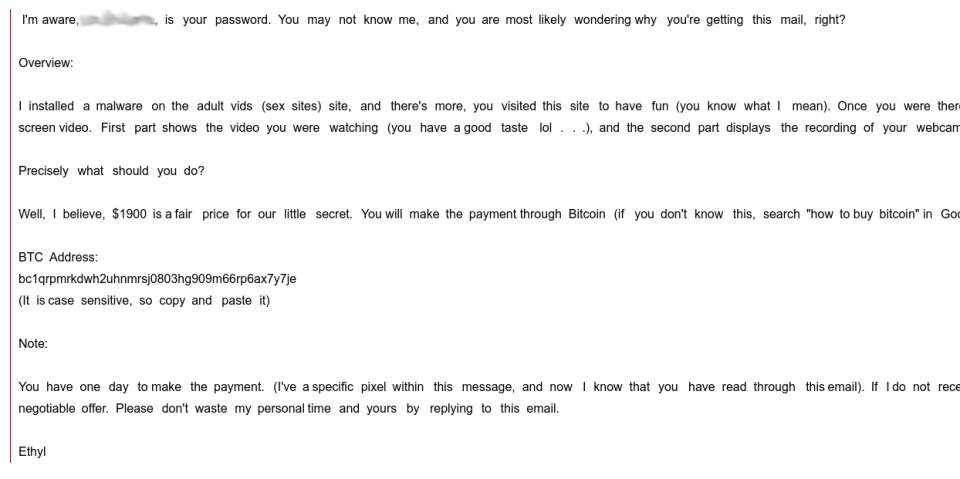
I just got a report of a scam attempt that did include a “proof”, so let's take a look at it:
Yes, the attacker knows your password. But they don't tell you to which service this password grants access to, which is pretty weird... If I were an asshole and had that information, I'd use it: at least to further prove to you that I know private shit about you, at worse to log in to that account, take it over and demand money for giving it back. And yet, they didn't. Suspicious.
But anyways... if you go to the ';--have i been pwned? website and enter your email, you'll see the list of data breaches over the years where your email was found.
This guy's email was in 18 of them. Some were connected to the same reused password. So here's how the attacker knew his password: he didn't hack his computer or gain access to his camera, he just found it (or bought it) on some shady website. The attacker probably doesn't even know what service was this password for or whether it's even still valid.
Good news about this attack: as of today, not a single cent was sent to
that BTC address
So what's the takeaway?
- Even if someone knows your password, it doesn't automatically prove their other claims.
- Sign up for email updates from ';--have i been pwned? and whenever they notify you about a breach, go to that website and change your password.
- Don't reuse passwords! The best way to stay secure is to use a different, strong, random password for each service
and store them in a password manager, like KeePass or even a browser.
If someone told me, they know that my password is
hiVxV788S2dm8rK6P5qH? Bitch, even I don't know that's my password
- Don't panic! The vast majority of such attacks is just a bluff.
 Avris
Avris
 Avris
Avris